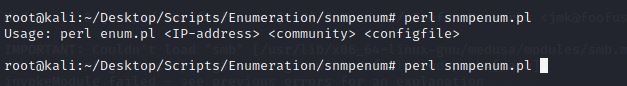
I was trying to use the snmpenum.pl in my lab and encountered this error.
Can't locate Net/SNMP.pm in @INC (you may need to install the Net::SNMP module)

I searched over the internet for the fix , but couldn't able to find something direct. However, going through some of the stackoverflow pages, i fixed it and is explained below.
2) Install the SNMP module for perl.
Can't locate Net/SNMP.pm in @INC (you may need to install the Net::SNMP module)
I searched over the internet for the fix , but couldn't able to find something direct. However, going through some of the stackoverflow pages, i fixed it and is explained below.
1) First install the required packages related to snmp utilities.
- sudo apt-get install libsnmp-perl

2) Install the SNMP module for perl.
- perl -MCPAN -e 'install Net::SNMP'

That's it. And i was able to run the script.